Proof cited in an eBook titled “AI Quantum Resilience”, printed by Utimaco [email wall], exhibits organisations think about safety dangers because the main barrier to efficient adoption of AI on knowledge they maintain.
AI’s worth is dependent upon knowledge amassed by an organisation. Nevertheless, there are safety dangers to constructing fashions and coaching them on that knowledge. These dangers are along with better-publicised threats to mental property that exist across the level of inference (immediate engineering, for instance).
The eBook’s authors state that organisations must handle threats all through their AI improvement and implementation processes. On the similar time, firms can and may put together to vary their safety protocols, adjustments that may develop into obligatory if quantum computing-powered decryption instruments develop into simply obtainable to unhealthy actors.
Utimaco lists three areas underneath risk:
- Coaching knowledge may be manipulated by unhealthy actors, degrading mannequin outputs in methods are onerous to detect,
- Fashions may be extracted or copied, eroding mental property rights,
- Delicate knowledge used throughout coaching or inference may be uncovered.
Present public key cryptography will develop into susceptible within the subsequent ten years, the report’s authors attest; a interval through which succesful quantum methods might emerge. Whatever the timescale, it’s thought that higher organised teams at present gather encrypted knowledge and retailer it to decrypt when or if quantum services develop into obtainable. Any dataset with long-term sensitivity, together with mannequin coaching knowledge, monetary information, or mental property, might require safety towards future decryption, due to this fact, Utimaco says.
A migration to quantum-resistant cryptography will have an effect on protocols, key administration, system interoperability, and efficiency, so any migration is more likely to take a number of years. The report’s authors counsel what they time period ‘crypto-agility’, which it defines as altering cryptographic algorithms with out redesigning underlying methods. ‘Crypto-agility’ relies on the precept of hybrid cryptography – combining established algorithms with post-quantum strategies, comparable to these prompt by NIST.
The eBook’s authors concur that cryptography by itself doesn’t handle all attainable areas of threat. It advocates the usage of hardware-based belief units that may isolate cryptographic keys and delicate operations from regular working environments.
If firms are creating their very own AI instruments and processes, safety on that foundation ought to prolong all through the AI lifecycle, from knowledge ingestion by way of to coaching, mannequin deployment, and inference in manufacturing. {Hardware} keys used to encrypt knowledge and signal fashions may be generated and saved inside a boundary. Mannequin integrity can then be verified earlier than deployment, and delicate knowledge processed throughout inference stays protected.
{Hardware}-based enclaves isolate workloads in order that even system directors with ample privileges can’t entry any of the info being processed. {Hardware} modules can confirm that the info enclave is in a trusted state earlier than releasing keys – a means of exterior attestation – serving to create a ‘chain of belief’ from {hardware} to utility.
{Hardware}-based key administration produces tamper-resistant logs overlaying entry and operations to help compliance frameworks such because the EU AI Act.
Most of the dangers inherent in AI methods are well-known if not already exploited. The danger from quantum computing’s capability to decrypt knowledge at present thought of secure is much less quick, however the implications ought to have an effect on knowledge and infrastructure selections made in the present day, Utimaco states. It advocates:
- A strengthening of controls all through the AI improvement and deployment lifecycle,
- The introduction of ‘crypto-agility’ to permit transition to post-quantum safety,
- Establishing hardware-based belief mechanisms wherever high-value property are in play.
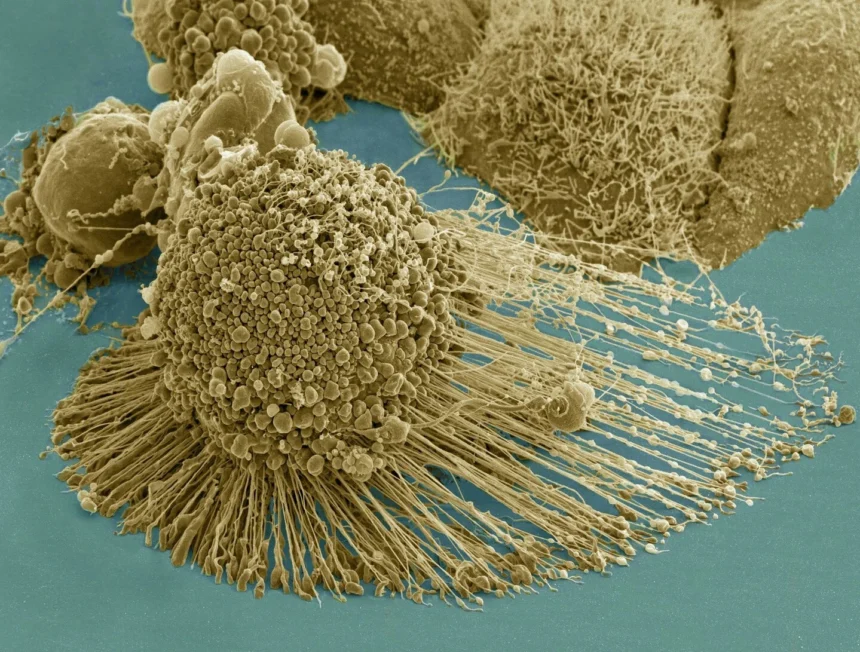
(Picture supply: “Scanning electron micrograph of an apoptotic HeLa cell” by Nationwide Institutes of Well being (NIH) is licensed underneath CC BY-NC 2.0. To view a duplicate of this license, go to https://creativecommons.org/licenses/by-nc/2.0)
Need to study extra about AI and large knowledge from business leaders? Take a look at AI & Big Data Expo happening in Amsterdam, California, and London. The excellent occasion is a part of TechEx and co-located with different main know-how occasions. Click on here for extra info.
AI Information is powered by TechForge Media. Discover different upcoming enterprise know-how occasions and webinars here.